CWE-401:Missing Release of Memory after Effective Lifetime
Weakness ID:401
Version:v4.17
Weakness Name:Missing Release of Memory after Effective Lifetime
Vulnerability Mapping:Allowed
Abstraction:Variant
Structure:Simple
Status:Draft
Likelihood of Exploit:Medium
▼Description
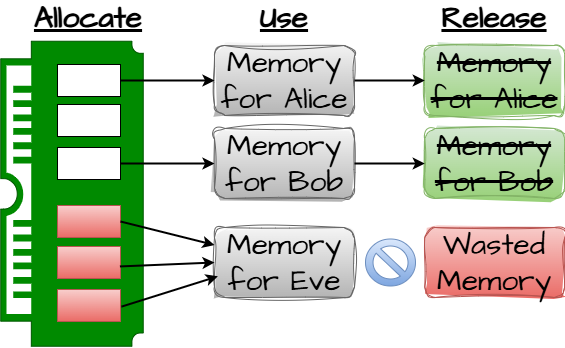
The product does not sufficiently track and release allocated memory after it has been used, making the memory unavailable for reallocation and reuse.
▼Extended Description
▼Alternate Terms
Memory Leak
▼Relationships
Relevant to the view"Research Concepts - (1000)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| ChildOf | Allowed | B | 772 | Missing Release of Resource after Effective Lifetime |
| ParentOf | Allowed | B | 390 | Detection of Error Condition Without Action |
Nature: ChildOf
Mapping: Allowed
Type: Base
ID: 772
▼Memberships
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 398 | 7PK - Code Quality |
| MemberOf | Prohibited | C | 730 | OWASP Top Ten 2004 Category A9 - Denial of Service |
| MemberOf | Prohibited | C | 861 | The CERT Oracle Secure Coding Standard for Java (2011) Chapter 18 - Miscellaneous (MSC) |
| MemberOf | Prohibited | C | 1152 | SEI CERT Oracle Secure Coding Standard for Java - Guidelines 49. Miscellaneous (MSC) |
| MemberOf | Prohibited | C | 1162 | SEI CERT C Coding Standard - Guidelines 08. Memory Management (MEM) |
| MemberOf | Prohibited | C | 1238 | SFP Primary Cluster: Failure to Release Memory |
| MemberOf | Prohibited | C | 1399 | Comprehensive Categorization: Memory Safety |
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 730
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 861
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1152
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1162
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1238
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1399
▼Tags
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | BS | BOSS-273 | Medium likelihood of exploit |
| MemberOf | Prohibited | BS | BOSS-278 | Libraries or Frameworks Strategy |
| MemberOf | Prohibited | BS | BOSS-313 | Reduce Performance (impact) |
| MemberOf | Prohibited | BS | BOSS-314 | DoS: Resource Consumption (CPU) (impact) |
| MemberOf | Prohibited | BS | BOSS-324 | DoS: Crash, Exit, or Restart (impact) |
| MemberOf | Prohibited | BS | BOSS-327 | DoS: Resource Consumption (Memory) (impact) |
| MemberOf | Prohibited | BS | BOSS-329 | DoS: Instability (impact) |
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-314
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-324
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-327
▼Relevant To View
Relevant to the view"Weaknesses Addressed by the SEI CERT Oracle Coding Standard for Java - (1133)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1152 | SEI CERT Oracle Secure Coding Standard for Java - Guidelines 49. Miscellaneous (MSC) |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 1152
Relevant to the view"Weaknesses Addressed by the SEI CERT C Coding Standard - (1154)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1162 | SEI CERT C Coding Standard - Guidelines 08. Memory Management (MEM) |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 1162
Relevant to the view"Software Fault Pattern (SFP) Clusters - (888)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1238 | SFP Primary Cluster: Failure to Release Memory |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 1238
Relevant to the view"Seven Pernicious Kingdoms - (700)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 398 | 7PK - Code Quality |
▼Background Detail
▼Common Consequences
| Scope | Likelihood | Impact | Note |
|---|---|---|---|
| Availability | N/A | DoS: Crash, Exit, or RestartDoS: InstabilityDoS: Resource Consumption (CPU)DoS: Resource Consumption (Memory) | Most memory leaks result in general product reliability problems, but if an attacker can intentionally trigger a memory leak, the attacker might be able to launch a denial of service attack (by crashing or hanging the program) or take advantage of other unexpected program behavior resulting from a low memory condition. |
| Other | N/A | Reduce Performance | N/A |
Scope: Availability
Likelihood: N/A
Impact: DoS: Crash, Exit, or Restart, DoS: Instability, DoS: Resource Consumption (CPU), DoS: Resource Consumption (Memory)
Note:
Most memory leaks result in general product reliability problems, but if an attacker can intentionally trigger a memory leak, the attacker might be able to launch a denial of service attack (by crashing or hanging the program) or take advantage of other unexpected program behavior resulting from a low memory condition.
Scope: Other
Likelihood: N/A
Impact: Reduce Performance
Note:
N/A
▼Potential Mitigations
Phase:Implementation
Mitigation ID: MIT-41
Strategy: Libraries or Frameworks
Effectiveness:
Description:
Choose a language or tool that provides automatic memory management, or makes manual memory management less error-prone.
For example, glibc in Linux provides protection against free of invalid pointers.
When using Xcode to target OS X or iOS, enable automatic reference counting (ARC) [REF-391].
To help correctly and consistently manage memory when programming in C++, consider using a smart pointer class such as std::auto_ptr (defined by ISO/IEC ISO/IEC 14882:2003), std::shared_ptr and std::unique_ptr (specified by an upcoming revision of the C++ standard, informally referred to as C++ 1x), or equivalent solutions such as Boost.
Note:
Phase:Architecture and Design
Mitigation ID:
Strategy:
Effectiveness:
Description:
Use an abstraction library to abstract away risky APIs. Not a complete solution.
Note:
Phase:Architecture and Design, Build and Compilation
Mitigation ID:
Strategy:
Effectiveness:
Description:
The Boehm-Demers-Weiser Garbage Collector or valgrind can be used to detect leaks in code.
Note:
This is not a complete solution as it is not 100% effective.
▼Modes Of Introduction
Phase: Implementation
Note:
Memory leaks have two common and sometimes overlapping causes:
- Error conditions and other exceptional circumstances often triggered by improper handling of malformed data or unexpectedly interrupted sessions.
- Confusion over which part of the program is responsible for freeing the memory, since in some languages, developers are responsible for tracking memory allocation and releasing the memory. If there are no more pointers or references to the memory, then it can no longer be tracked and identified for release.
▼Applicable Platforms
Languages
Class: C(Undetermined Prevalence)
Class: C++(Undetermined Prevalence)
▼Demonstrative Examples
Example 1
The following C function leaks a block of allocated memory if the call to read() does not return the expected number of bytes:
Language: ( code)
N/A
Language: C(Bad code)
char* getBlock(int fd) {
char* buf = (char*) malloc(BLOCK_SIZE);
if (!buf) {
return NULL;
}
if (read(fd, buf, BLOCK_SIZE) != BLOCK_SIZE) {
return NULL;
}
return buf;
}
▼Observed Examples
| Reference | Description |
|---|---|
| CVE-2005-3119 | Memory leak because function does not free() an element of a data structure. |
| CVE-2004-0427 | Memory leak when counter variable is not decremented. |
| CVE-2002-0574 | chain: reference count is not decremented, leading to memory leak in OS by sending ICMP packets. |
| CVE-2005-3181 | Kernel uses wrong function to release a data structure, preventing data from being properly tracked by other code. |
| CVE-2004-0222 | Memory leak via unknown manipulations as part of protocol test suite. |
| CVE-2001-0136 | Memory leak via a series of the same command. |
Reference: CVE-2005-3119
Description:
Memory leak because function does not free() an element of a data structure.
Reference: CVE-2004-0427
Description:
Memory leak when counter variable is not decremented.
Reference: CVE-2002-0574
Description:
chain: reference count is not decremented, leading to memory leak in OS by sending ICMP packets.
Reference: CVE-2005-3181
Description:
Kernel uses wrong function to release a data structure, preventing data from being properly tracked by other code.
Reference: CVE-2004-0222
Description:
Memory leak via unknown manipulations as part of protocol test suite.
Reference: CVE-2001-0136
Description:
Memory leak via a series of the same command.
▼Affected Resources
- Memory
▼Functional Areas
- Memory Management
▼Weakness Ordinalities
| Ordinality | Description |
|---|---|
| Resultant | N/A |
Ordinality: Resultant
Description:
N/A
▼Detection Methods
Fuzzing
Detection Method ID:DM-13
Description:
Fuzz testing (fuzzing) is a powerful technique for generating large numbers of diverse inputs - either randomly or algorithmically - and dynamically invoking the code with those inputs. Even with random inputs, it is often capable of generating unexpected results such as crashes, memory corruption, or resource consumption. Fuzzing effectively produces repeatable test cases that clearly indicate bugs, which helps developers to diagnose the issues.
Effectiveness:High
Note:
N/A
Automated Static Analysis
Detection Method ID:DM-14
Description:
Automated static analysis, commonly referred to as Static Application Security Testing (SAST), can find some instances of this weakness by analyzing source code (or binary/compiled code) without having to execute it. Typically, this is done by building a model of data flow and control flow, then searching for potentially-vulnerable patterns that connect "sources" (origins of input) with "sinks" (destinations where the data interacts with external components, a lower layer such as the OS, etc.)
Effectiveness:High
Note:
N/A
▼Vulnerability Mapping Notes
Usage:Allowed
Reason:Acceptable-Use
Rationale:
This CWE entry is at the Variant level of abstraction, which is a preferred level of abstraction for mapping to the root causes of vulnerabilities.
Comments:
Carefully read both the name and description to ensure that this mapping is an appropriate fit. Do not try to 'force' a mapping to a lower-level Base/Variant simply to comply with this preferred level of abstraction.
Suggestions:
▼Notes
Relationship
This is often a resultant weakness due to improper handling of malformed data or early termination of sessions.
N/A
Terminology
"memory leak" has sometimes been used to describe other kinds of issues, e.g. for information leaks in which the contents of memory are inadvertently leaked (CVE-2003-0400 is one such example of this terminology conflict).
N/A
▼Taxonomy Mappings
| Taxonomy Name | Entry ID | Fit | Entry Name |
|---|---|---|---|
| PLOVER | N/A | N/A | Memory leak |
| 7 Pernicious Kingdoms | N/A | N/A | Memory Leak |
| CLASP | N/A | N/A | Failure to deallocate data |
| OWASP Top Ten 2004 | A9 | CWE More Specific | Denial of Service |
| CERT C Secure Coding | MEM31-C | Exact | Free dynamically allocated memory when no longer needed |
| The CERT Oracle Secure Coding Standard for Java (2011) | MSC04-J | N/A | Do not leak memory |
| Software Fault Patterns | SFP14 | N/A | Failure to Release Resource |
| OMG ASCPEM | ASCPEM-PRF-14 | N/A | N/A |
Taxonomy Name: PLOVER
Entry ID: N/A
Fit: N/A
Entry Name: Memory leak
Taxonomy Name: 7 Pernicious Kingdoms
Entry ID: N/A
Fit: N/A
Entry Name: Memory Leak
Taxonomy Name: CLASP
Entry ID: N/A
Fit: N/A
Entry Name: Failure to deallocate data
Taxonomy Name: OWASP Top Ten 2004
Entry ID: A9
Fit: CWE More Specific
Entry Name: Denial of Service
Taxonomy Name: CERT C Secure Coding
Entry ID: MEM31-C
Fit: Exact
Entry Name: Free dynamically allocated memory when no longer needed
Taxonomy Name: The CERT Oracle Secure Coding Standard for Java (2011)
Entry ID: MSC04-J
Fit: N/A
Entry Name: Do not leak memory
Taxonomy Name: Software Fault Patterns
Entry ID: SFP14
Fit: N/A
Entry Name: Failure to Release Resource
Taxonomy Name: OMG ASCPEM
Entry ID: ASCPEM-PRF-14
Fit: N/A
Entry Name: N/A
▼Related Attack Patterns
| ID | Name |
|---|
▼References
Reference ID: REF-18
Title: The CLASP Application Security Process
Author: Secure Software, Inc.
Section:
Publication:
Publisher:
Edition:
URL Date:2024-11-17
Day:N/A
Month:N/A
Year:2005
Reference ID: REF-390
Title: How to Break Software Security
Author: J. Whittaker, H. Thompson
Section:
Publication:
Publisher:Addison Wesley
Edition:
URL:
URL Date:
Day:N/A
Month:N/A
Year:2003
Reference ID: REF-391
Title: Transitioning to ARC Release Notes
Author: iOS Developer Library
Section:
Publication:
Publisher:
Edition:
URL Date:2023-04-07
Day:08
Month:08
Year:2013
Reference ID: REF-959
Title: Automated Source Code Performance Efficiency Measure (ASCPEM)
Author: Object Management Group (OMG)
Section: ASCPEM-PRF-14
Publication:
Details not found