CWE-89:Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')
Weakness ID:89
Version:v4.17
Weakness Name:Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')
Vulnerability Mapping:Allowed
Abstraction:Base
Structure:Simple
Status:Stable
Likelihood of Exploit:High
▼Description
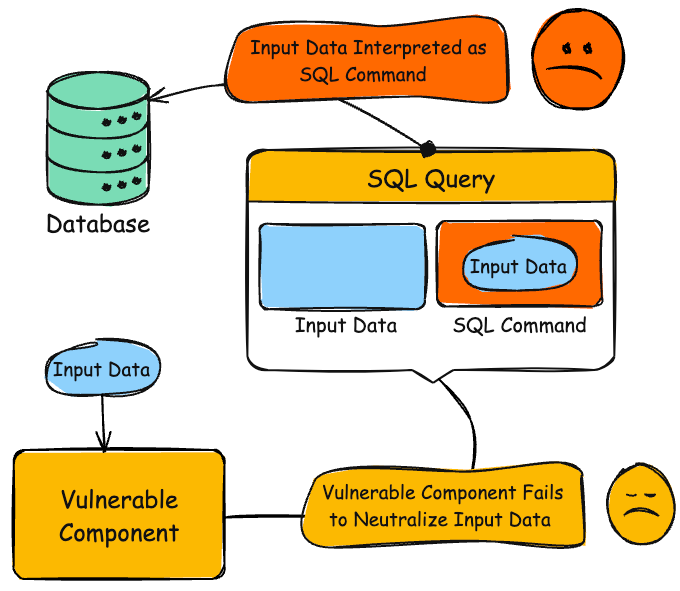
The product constructs all or part of an SQL command using externally-influenced input from an upstream component, but it does not neutralize or incorrectly neutralizes special elements that could modify the intended SQL command when it is sent to a downstream component. Without sufficient removal or quoting of SQL syntax in user-controllable inputs, the generated SQL query can cause those inputs to be interpreted as SQL instead of ordinary user data.
▼Extended Description
▼Alternate Terms
SQL injection
a common attack-oriented phrase
SQLi
a common abbreviation for "SQL injection"
▼Relationships
Relevant to the view"Research Concepts - (1000)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| ChildOf | Allowed-with-Review | C | 943 | Improper Neutralization of Special Elements in Data Query Logic |
| ParentOf | Allowed | V | 456 | Missing Initialization of a Variable |
| ParentOf | Allowed | V | 564 | SQL Injection: Hibernate |
Nature: ChildOf
Mapping: Allowed-with-Review
Type: Class
ID: 943
▼Memberships
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 635
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 713
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 722
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 727
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 751
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 801
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 810
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 864
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 929
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 990
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1005
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1027
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1131
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 1200
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 1337
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1347
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 1350
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 1387
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1409
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 1425
Nature: MemberOf
Mapping: Prohibited
Type:View
ID: 1430
▼Tags
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | BS | BOSS-240 | Weaknesses in Software Written in SQL |
| MemberOf | Prohibited | BS | BOSS-272 | Weaknesses in Database Server |
| MemberOf | Prohibited | BS | BOSS-274 | High likelihood of exploit |
| MemberOf | Prohibited | BS | BOSS-276 | Environment Hardening Strategy |
| MemberOf | Prohibited | BS | BOSS-278 | Libraries or Frameworks Strategy |
| MemberOf | Prohibited | BS | BOSS-279 | Input Validation Strategy |
| MemberOf | Prohibited | BS | BOSS-282 | Parameterization Strategy |
| MemberOf | Prohibited | BS | BOSS-284 | Output Encoding Strategy |
| MemberOf | Prohibited | BS | BOSS-285 | Firewall Strategy |
| MemberOf | Prohibited | BS | BOSS-287 | Enforcement by Conversion Strategy |
| MemberOf | Prohibited | BS | BOSS-294 | Not Language-Specific Weaknesses |
| MemberOf | Prohibited | BS | BOSS-311 | Execute Unauthorized Code or Commands (impact) |
| MemberOf | Prohibited | BS | BOSS-316 | Bypass Protection Mechanism (impact) |
| MemberOf | Prohibited | BS | BOSS-318 | Modify Application Data (impact) |
| MemberOf | Prohibited | BS | BOSS-328 | Read Application Data (impact) |
| MemberOf | Prohibited | BS | BOSS-332 | Gain Privileges or Assume Identity (impact) |
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-240
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-287
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-311
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-316
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-332
▼Relevant To View
Relevant to the view"Seven Pernicious Kingdoms - (700)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1005 | 7PK - Input Validation and Representation |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 1005
Relevant to the view"Architectural Concepts - (1008)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1019 | Validate Inputs |
Relevant to the view"CISQ Quality Measures (2020) - (1305)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1308 | CISQ Quality Measures - Security |
Relevant to the view"OWASP Top Ten (2021) - (1344)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1347 | OWASP Top Ten 2021 Category A03:2021 - Injection |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 1347
Relevant to the view"Software Development - (699)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 137 | Data Neutralization Issues |
Relevant to the view"Software Fault Pattern (SFP) Clusters - (888)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 990 | SFP Secondary Cluster: Tainted Input to Command |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 990
▼Background Detail
▼Common Consequences
| Scope | Likelihood | Impact | Note |
|---|---|---|---|
| ConfidentialityIntegrityAvailability | N/A | Execute Unauthorized Code or Commands | Adversaries could execute system commands, typically by changing the SQL statement to redirect output to a file that can then be executed. |
| Confidentiality | N/A | Read Application Data | Since SQL databases generally hold sensitive data, loss of confidentiality is a frequent problem with SQL injection vulnerabilities. |
| Authentication | N/A | Gain Privileges or Assume IdentityBypass Protection Mechanism | If poor SQL commands are used to check user names and passwords or perform other kinds of authentication, it may be possible to connect to the product as another user with no previous knowledge of the password. |
| Access Control | N/A | Bypass Protection Mechanism | If authorization information is held in a SQL database, it may be possible to change this information through the successful exploitation of a SQL injection vulnerability. |
| Integrity | N/A | Modify Application Data | Just as it may be possible to read sensitive information, it is also possible to modify or even delete this information with a SQL injection attack. |
Scope: Confidentiality, Integrity, Availability
Likelihood: N/A
Impact: Execute Unauthorized Code or Commands
Note:
Adversaries could execute system commands, typically by changing the SQL statement to redirect output to a file that can then be executed.
Scope: Confidentiality
Likelihood: N/A
Impact: Read Application Data
Note:
Since SQL databases generally hold sensitive data, loss of confidentiality is a frequent problem with SQL injection vulnerabilities.
Scope: Authentication
Likelihood: N/A
Impact: Gain Privileges or Assume Identity, Bypass Protection Mechanism
Note:
If poor SQL commands are used to check user names and passwords or perform other kinds of authentication, it may be possible to connect to the product as another user with no previous knowledge of the password.
Scope: Access Control
Likelihood: N/A
Impact: Bypass Protection Mechanism
Note:
If authorization information is held in a SQL database, it may be possible to change this information through the successful exploitation of a SQL injection vulnerability.
Scope: Integrity
Likelihood: N/A
Impact: Modify Application Data
Note:
Just as it may be possible to read sensitive information, it is also possible to modify or even delete this information with a SQL injection attack.
▼Potential Mitigations
Phase:Architecture and Design
Mitigation ID: MIT-4
Strategy: Libraries or Frameworks
Effectiveness:
Description:
Use a vetted library or framework that does not allow this weakness to occur or provides constructs that make this weakness easier to avoid.
For example, consider using persistence layers such as Hibernate or Enterprise Java Beans, which can provide significant protection against SQL injection if used properly.
Note:
Phase:Architecture and Design
Mitigation ID: MIT-27
Strategy: Parameterization
Effectiveness:
Description:
If available, use structured mechanisms that automatically enforce the separation between data and code. These mechanisms may be able to provide the relevant quoting, encoding, and validation automatically, instead of relying on the developer to provide this capability at every point where output is generated.
Process SQL queries using prepared statements, parameterized queries, or stored procedures. These features should accept parameters or variables and support strong typing. Do not dynamically construct and execute query strings within these features using "exec" or similar functionality, since this may re-introduce the possibility of SQL injection. [REF-867]
Note:
Phase:Architecture and Design, Operation
Mitigation ID: MIT-17
Strategy: Environment Hardening
Effectiveness:
Description:
Run your code using the lowest privileges that are required to accomplish the necessary tasks [REF-76]. If possible, create isolated accounts with limited privileges that are only used for a single task. That way, a successful attack will not immediately give the attacker access to the rest of the software or its environment. For example, database applications rarely need to run as the database administrator, especially in day-to-day operations.
Specifically, follow the principle of least privilege when creating user accounts to a SQL database. The database users should only have the minimum privileges necessary to use their account. If the requirements of the system indicate that a user can read and modify their own data, then limit their privileges so they cannot read/write others' data. Use the strictest permissions possible on all database objects, such as execute-only for stored procedures.
Note:
Phase:Architecture and Design
Mitigation ID: MIT-15
Strategy:
Effectiveness:
Description:
For any security checks that are performed on the client side, ensure that these checks are duplicated on the server side, in order to avoid CWE-602. Attackers can bypass the client-side checks by modifying values after the checks have been performed, or by changing the client to remove the client-side checks entirely. Then, these modified values would be submitted to the server.
Note:
Phase:Implementation
Mitigation ID: MIT-28
Strategy: Output Encoding
Effectiveness:
Description:
While it is risky to use dynamically-generated query strings, code, or commands that mix control and data together, sometimes it may be unavoidable. Properly quote arguments and escape any special characters within those arguments. The most conservative approach is to escape or filter all characters that do not pass an extremely strict allowlist (such as everything that is not alphanumeric or white space). If some special characters are still needed, such as white space, wrap each argument in quotes after the escaping/filtering step. Be careful of argument injection (CWE-88).
Instead of building a new implementation, such features may be available in the database or programming language. For example, the Oracle DBMS_ASSERT package can check or enforce that parameters have certain properties that make them less vulnerable to SQL injection. For MySQL, the mysql_real_escape_string() API function is available in both C and PHP.
Note:
Phase:Implementation
Mitigation ID: MIT-5
Strategy: Input Validation
Effectiveness:
Description:
Assume all input is malicious. Use an "accept known good" input validation strategy, i.e., use a list of acceptable inputs that strictly conform to specifications. Reject any input that does not strictly conform to specifications, or transform it into something that does.
When performing input validation, consider all potentially relevant properties, including length, type of input, the full range of acceptable values, missing or extra inputs, syntax, consistency across related fields, and conformance to business rules. As an example of business rule logic, "boat" may be syntactically valid because it only contains alphanumeric characters, but it is not valid if the input is only expected to contain colors such as "red" or "blue."
Do not rely exclusively on looking for malicious or malformed inputs. This is likely to miss at least one undesirable input, especially if the code's environment changes. This can give attackers enough room to bypass the intended validation. However, denylists can be useful for detecting potential attacks or determining which inputs are so malformed that they should be rejected outright.
When constructing SQL query strings, use stringent allowlists that limit the character set based on the expected value of the parameter in the request. This will indirectly limit the scope of an attack, but this technique is less important than proper output encoding and escaping.
Note that proper output encoding, escaping, and quoting is the most effective solution for preventing SQL injection, although input validation may provide some defense-in-depth. This is because it effectively limits what will appear in output. Input validation will not always prevent SQL injection, especially if you are required to support free-form text fields that could contain arbitrary characters. For example, the name "O'Reilly" would likely pass the validation step, since it is a common last name in the English language. However, it cannot be directly inserted into the database because it contains the "'" apostrophe character, which would need to be escaped or otherwise handled. In this case, stripping the apostrophe might reduce the risk of SQL injection, but it would produce incorrect behavior because the wrong name would be recorded.
When feasible, it may be safest to disallow meta-characters entirely, instead of escaping them. This will provide some defense in depth. After the data is entered into the database, later processes may neglect to escape meta-characters before use, and you may not have control over those processes.
Note:
Phase:Architecture and Design
Mitigation ID: MIT-21
Strategy: Enforcement by Conversion
Effectiveness:
Description:
When the set of acceptable objects, such as filenames or URLs, is limited or known, create a mapping from a set of fixed input values (such as numeric IDs) to the actual filenames or URLs, and reject all other inputs.
Note:
Phase:Implementation
Mitigation ID: MIT-39
Strategy:
Effectiveness:
Description:
Ensure that error messages only contain minimal details that are useful to the intended audience and no one else. The messages need to strike the balance between being too cryptic (which can confuse users) or being too detailed (which may reveal more than intended). The messages should not reveal the methods that were used to determine the error. Attackers can use detailed information to refine or optimize their original attack, thereby increasing their chances of success.
If errors must be captured in some detail, record them in log messages, but consider what could occur if the log messages can be viewed by attackers. Highly sensitive information such as passwords should never be saved to log files.
Avoid inconsistent messaging that might accidentally tip off an attacker about internal state, such as whether a user account exists or not.
In the context of SQL Injection, error messages revealing the structure of a SQL query can help attackers tailor successful attack strings.
Note:
Phase:Operation
Mitigation ID: MIT-29
Strategy: Firewall
Effectiveness: Moderate
Description:
Use an application firewall that can detect attacks against this weakness. It can be beneficial in cases in which the code cannot be fixed (because it is controlled by a third party), as an emergency prevention measure while more comprehensive software assurance measures are applied, or to provide defense in depth.
Note:
An application firewall might not cover all possible input vectors. In addition, attack techniques might be available to bypass the protection mechanism, such as using malformed inputs that can still be processed by the component that receives those inputs. Depending on functionality, an application firewall might inadvertently reject or modify legitimate requests. Finally, some manual effort may be required for customization.
Phase:Operation, Implementation
Mitigation ID: MIT-16
Strategy: Environment Hardening
Effectiveness:
Description:
When using PHP, configure the application so that it does not use register_globals. During implementation, develop the application so that it does not rely on this feature, but be wary of implementing a register_globals emulation that is subject to weaknesses such as CWE-95, CWE-621, and similar issues.
Note:
▼Modes Of Introduction
Phase: Implementation
Note:
REALIZATION: This weakness is caused during implementation of an architectural security tactic.
Phase: Implementation
Note:
This weakness typically appears in data-rich applications that save user inputs in a database.
▼Applicable Platforms
Languages
Class: Not Language-Specific(Undetermined Prevalence)
Class: SQL(Often Prevalence)
Technology
Class: Database Server(Undetermined Prevalence)
▼Demonstrative Examples
Example 1
In 2008, a large number of web servers were compromised using the same SQL injection attack string. This single string worked against many different programs. The SQL injection was then used to modify the web sites to serve malicious code.
Language: ( code)
N/A
Example 2
The following code dynamically constructs and executes a SQL query that searches for items matching a specified name. The query restricts the items displayed to those where owner matches the user name of the currently-authenticated user.
Language: ( code)
N/A
Language: C#(Bad code)
...
string userName = ctx.getAuthenticatedUserName();
string query = "SELECT * FROM items WHERE owner = '" + userName + "' AND itemname = '" + ItemName.Text + "'";
sda = new SqlDataAdapter(query, conn);
DataTable dt = new DataTable();
sda.Fill(dt);
...
Language: ( code)
N/A
The query that this code intends to execute follows:
Language: (Informative code)
SELECT * FROM items WHERE owner = <userName> AND itemname = <itemName>;
Language: ( code)
N/A
However, because the query is constructed dynamically by concatenating a constant base query string and a user input string, the query only behaves correctly if itemName does not contain a single-quote character. If an attacker with the user name wiley enters the string:
Language: (Attack code)
name' OR 'a'='a
Language: ( code)
N/A
for itemName, then the query becomes the following:
Language: (Attack code)
SELECT * FROM items WHERE owner = 'wiley' AND itemname = 'name' OR 'a'='a';
Language: ( code)
N/A
The addition of the:
Language: (Attack code)
OR 'a'='a
Language: ( code)
N/A
condition causes the WHERE clause to always evaluate to true, so the query becomes logically equivalent to the much simpler query:
Language: (Attack code)
SELECT * FROM items;
Language: ( code)
N/A
This simplification of the query allows the attacker to bypass the requirement that the query only return items owned by the authenticated user; the query now returns all entries stored in the items table, regardless of their specified owner.
Example 3
This example examines the effects of a different malicious value passed to the query constructed and executed in the previous example.
Language: ( code)
N/A
Language: ( code)
N/A
If an attacker with the user name wiley enters the string:
Language: (Attack code)
name'; DELETE FROM items; --
Language: ( code)
N/A
for itemName, then the query becomes the following two queries:
Language: SQL(Attack code)
SELECT * FROM items WHERE owner = 'wiley' AND itemname = 'name';
DELETE FROM items;
--'*
Language: ( code)
N/A
Many database servers, including Microsoft(R) SQL Server 2000, allow multiple SQL statements separated by semicolons to be executed at once. While this attack string results in an error on Oracle and other database servers that do not allow the batch-execution of statements separated by semicolons, on databases that do allow batch execution, this type of attack allows the attacker to execute arbitrary commands against the database.
Language: ( code)
N/A
Notice the trailing pair of hyphens (--), which specifies to most database servers that the remainder of the statement is to be treated as a comment and not executed. In this case the comment character serves to remove the trailing single-quote left over from the modified query. On a database where comments are not allowed to be used in this way, the general attack could still be made effective using a trick similar to the one shown in the previous example.
Language: ( code)
N/A
If an attacker enters the string
Language: (Attack code)
name'; DELETE FROM items; SELECT * FROM items WHERE 'a'='a
Language: ( code)
N/A
Then the following three valid statements will be created:
Language: (Attack code)
SELECT * FROM items WHERE owner = 'wiley' AND itemname = 'name';
DELETE FROM items;
SELECT * FROM items WHERE 'a'='a';
Language: ( code)
N/A
One traditional approach to preventing SQL injection attacks is to handle them as an input validation problem and either accept only characters from an allowlist of safe values or identify and escape a denylist of potentially malicious values. Allowlists can be a very effective means of enforcing strict input validation rules, but parameterized SQL statements require less maintenance and can offer more guarantees with respect to security. As is almost always the case, denylisting is riddled with loopholes that make it ineffective at preventing SQL injection attacks. For example, attackers can:
Language: ( code)
N/A
- Target fields that are not quoted
- Find ways to bypass the need for certain escaped meta-characters
- Use stored procedures to hide the injected meta-characters.
Language: ( code)
N/A
Manually escaping characters in input to SQL queries can help, but it will not make your application secure from SQL injection attacks.
Language: ( code)
N/A
Another solution commonly proposed for dealing with SQL injection attacks is to use stored procedures. Although stored procedures prevent some types of SQL injection attacks, they do not protect against many others. For example, the following PL/SQL procedure is vulnerable to the same SQL injection attack shown in the first example.
Language: SQL(Bad code)
procedure get_item ( itm_cv IN OUT ItmCurTyp, usr in varchar2, itm in varchar2)
is open itm_cv for
' SELECT * FROM items WHERE ' || 'owner = '|| usr || ' AND itemname = ' || itm || ';
end get_item;
Language: ( code)
N/A
Stored procedures typically help prevent SQL injection attacks by limiting the types of statements that can be passed to their parameters. However, there are many ways around the limitations and many interesting statements that can still be passed to stored procedures. Again, stored procedures can prevent some exploits, but they will not make your application secure against SQL injection attacks.
Example 4
MS SQL has a built in function that enables shell command execution. An SQL injection in such a context could be disastrous. For example, a query of the form:
Language: ( code)
N/A
Language: SQL(Bad code)
SELECT ITEM,PRICE FROM PRODUCT WHERE ITEM_CATEGORY='$user_input' ORDER BY PRICE
Language: ( code)
N/A
Where $user_input is taken from an untrusted source.
Language: ( code)
N/A
If the user provides the string:
Language: (Attack code)
'; exec master..xp_cmdshell 'dir' --
Language: ( code)
N/A
The query will take the following form:
Language: (Attack code)
SELECT ITEM,PRICE FROM PRODUCT WHERE ITEM_CATEGORY=''; exec master..xp_cmdshell 'dir' --' ORDER BY PRICE
Language: ( code)
N/A
Now, this query can be broken down into:
Language: ( code)
N/A
- a first SQL query: SELECT ITEM,PRICE FROM PRODUCT WHERE ITEM_CATEGORY='';
- a second SQL query, which executes the dir command in the shell: exec master..xp_cmdshell 'dir'
- an MS SQL comment: --' ORDER BY PRICE
Language: ( code)
N/A
As can be seen, the malicious input changes the semantics of the query into a query, a shell command execution and a comment.
Example 5
This code intends to print a message summary given the message ID.
Language: ( code)
N/A
Language: PHP(Bad code)
$id = $_COOKIE["mid"];
mysql_query("SELECT MessageID, Subject FROM messages WHERE MessageID = '$id'");
Language: ( code)
N/A
The programmer may have skipped any input validation on $id under the assumption that attackers cannot modify the cookie. However, this is easy to do with custom client code or even in the web browser.
Language: ( code)
N/A
While $id is wrapped in single quotes in the call to mysql_query(), an attacker could simply change the incoming mid cookie to:
Language: (Attack code)
1432' or '1' = '1
Language: ( code)
N/A
This would produce the resulting query:
Language: (Result code)
SELECT MessageID, Subject FROM messages WHERE MessageID = '1432' or '1' = '1'
Language: ( code)
N/A
Not only will this retrieve message number 1432, it will retrieve all other messages.
Language: ( code)
N/A
In this case, the programmer could apply a simple modification to the code to eliminate the SQL injection:
Language: PHP(Good code)
$id = intval($_COOKIE["mid"]);
mysql_query("SELECT MessageID, Subject FROM messages WHERE MessageID = '$id'");
Language: ( code)
N/A
However, if this code is intended to support multiple users with different message boxes, the code might also need an access control check (CWE-285) to ensure that the application user has the permission to see that message.
Example 6
This example attempts to take a last name provided by a user and enter it into a database.
Language: ( code)
N/A
Language: Perl(Bad code)
$userKey = getUserID();
$name = getUserInput();
# ensure only letters, hyphens and apostrophe are allowed*
$name = allowList($name, "^a-zA-z'-$");
$query = "INSERT INTO last_names VALUES('$userKey', '$name')";
Language: ( code)
N/A
While the programmer applies an allowlist to the user input, it has shortcomings. First of all, the user is still allowed to provide hyphens, which are used as comment structures in SQL. If a user specifies "--" then the remainder of the statement will be treated as a comment, which may bypass security logic. Furthermore, the allowlist permits the apostrophe, which is also a data / command separator in SQL. If a user supplies a name with an apostrophe, they may be able to alter the structure of the whole statement and even change control flow of the program, possibly accessing or modifying confidential information. In this situation, both the hyphen and apostrophe are legitimate characters for a last name and permitting them is required. Instead, a programmer may want to use a prepared statement or apply an encoding routine to the input to prevent any data / directive misinterpretations.
▼Observed Examples
| Reference | Description |
|---|---|
| CVE-2023-32530 | SQL injection in security product dashboard using crafted certificate fields |
| CVE-2021-42258 | SQL injection in time and billing software, as exploited in the wild per CISA KEV. |
| CVE-2021-27101 | SQL injection in file-transfer system via a crafted Host header, as exploited in the wild per CISA KEV. |
| CVE-2020-12271 | SQL injection in firewall product's admin interface or user portal, as exploited in the wild per CISA KEV. |
| CVE-2019-3792 | An automation system written in Go contains an API that is vulnerable to SQL injection allowing the attacker to read privileged data. |
| CVE-2004-0366 | chain: SQL injection in library intended for database authentication allows SQL injection and authentication bypass. |
| CVE-2008-2790 | SQL injection through an ID that was supposed to be numeric. |
| CVE-2008-2223 | SQL injection through an ID that was supposed to be numeric. |
| CVE-2007-6602 | SQL injection via user name. |
| CVE-2008-5817 | SQL injection via user name or password fields. |
| CVE-2003-0377 | SQL injection in security product, using a crafted group name. |
| CVE-2008-2380 | SQL injection in authentication library. |
| CVE-2017-11508 | SQL injection in vulnerability management and reporting tool, using a crafted password. |
Reference: CVE-2023-32530
Description:
SQL injection in security product dashboard using crafted certificate fields
Reference: CVE-2021-42258
Description:
SQL injection in time and billing software, as exploited in the wild per CISA KEV.
Reference: CVE-2021-27101
Description:
SQL injection in file-transfer system via a crafted Host header, as exploited in the wild per CISA KEV.
Reference: CVE-2020-12271
Description:
SQL injection in firewall product's admin interface or user portal, as exploited in the wild per CISA KEV.
Reference: CVE-2019-3792
Description:
An automation system written in Go contains an API that is vulnerable to SQL injection allowing the attacker to read privileged data.
Reference: CVE-2004-0366
Description:
chain: SQL injection in library intended for database authentication allows SQL injection and authentication bypass.
Reference: CVE-2008-2790
Description:
SQL injection through an ID that was supposed to be numeric.
Reference: CVE-2008-2223
Description:
SQL injection through an ID that was supposed to be numeric.
Reference: CVE-2007-6602
Description:
SQL injection via user name.
Reference: CVE-2008-5817
Description:
SQL injection via user name or password fields.
Reference: CVE-2003-0377
Description:
SQL injection in security product, using a crafted group name.
Reference: CVE-2008-2380
Description:
SQL injection in authentication library.
Reference: CVE-2017-11508
Description:
SQL injection in vulnerability management and reporting tool, using a crafted password.
▼Affected Resources
▼Functional Areas
▼Weakness Ordinalities
| Ordinality | Description |
|---|
▼Detection Methods
Automated Static Analysis
Detection Method ID:DM-1
Description:
This weakness can often be detected using automated static analysis tools. Many modern tools use data flow analysis or constraint-based techniques to minimize the number of false positives.
Automated static analysis might not be able to recognize when proper input validation is being performed, leading to false positives - i.e., warnings that do not have any security consequences or do not require any code changes.
Automated static analysis might not be able to detect the usage of custom API functions or third-party libraries that indirectly invoke SQL commands, leading to false negatives - especially if the API/library code is not available for analysis.
Effectiveness:
Note:
This is not a perfect solution, since 100% accuracy and coverage are not feasible.
Automated Dynamic Analysis
Detection Method ID:DM-2
Description:
This weakness can be detected using dynamic tools and techniques that interact with the software using large test suites with many diverse inputs, such as fuzz testing (fuzzing), robustness testing, and fault injection. The software's operation may slow down, but it should not become unstable, crash, or generate incorrect results.
Effectiveness:Moderate
Note:
N/A
Manual Analysis
Detection Method ID:DM-9
Description:
Manual analysis can be useful for finding this weakness, but it might not achieve desired code coverage within limited time constraints. This becomes difficult for weaknesses that must be considered for all inputs, since the attack surface can be too large.
Effectiveness:
Note:
N/A
Automated Static Analysis - Binary or Bytecode
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Bytecode Weakness Analysis - including disassembler + source code weakness analysis Binary Weakness Analysis - including disassembler + source code weakness analysis
Effectiveness:High
Note:
N/A
Dynamic Analysis with Automated Results Interpretation
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Database Scanners ``` Cost effective for partial coverage: ```
Web Application Scanner Web Services Scanner
Effectiveness:High
Note:
N/A
Dynamic Analysis with Manual Results Interpretation
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Cost effective for partial coverage: ```
Fuzz Tester Framework-based Fuzzer
Effectiveness:SOAR Partial
Note:
N/A
Manual Static Analysis - Source Code
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Manual Source Code Review (not inspections) ``` Cost effective for partial coverage: ```
Focused Manual Spotcheck - Focused manual analysis of source
Effectiveness:High
Note:
N/A
Automated Static Analysis - Source Code
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Source code Weakness Analyzer Context-configured Source Code Weakness Analyzer
Effectiveness:High
Note:
N/A
Architecture or Design Review
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Formal Methods / Correct-By-Construction ``` Cost effective for partial coverage: ```
Inspection (IEEE 1028 standard) (can apply to requirements, design, source code, etc.)
Effectiveness:High
Note:
N/A
▼Vulnerability Mapping Notes
Usage:Allowed
Reason:Acceptable-Use
Rationale:
This CWE entry is at the Base level of abstraction, which is a preferred level of abstraction for mapping to the root causes of vulnerabilities.
Comments:
Carefully read both the name and description to ensure that this mapping is an appropriate fit. Do not try to 'force' a mapping to a lower-level Base/Variant simply to comply with this preferred level of abstraction.
Suggestions:
▼Notes
Relationship
SQL injection can be resultant from special character mismanagement, MAID, or denylist/allowlist problems. It can be primary to authentication errors.
N/A
▼Taxonomy Mappings
| Taxonomy Name | Entry ID | Fit | Entry Name |
|---|---|---|---|
| PLOVER | N/A | N/A | SQL injection |
| 7 Pernicious Kingdoms | N/A | N/A | SQL Injection |
| CLASP | N/A | N/A | SQL injection |
| OWASP Top Ten 2007 | A2 | CWE More Specific | Injection Flaws |
| OWASP Top Ten 2004 | A1 | CWE More Specific | Unvalidated Input |
| OWASP Top Ten 2004 | A6 | CWE More Specific | Injection Flaws |
| WASC | 19 | N/A | SQL Injection |
| Software Fault Patterns | SFP24 | N/A | Tainted input to command |
| OMG ASCSM | ASCSM-CWE-89 | N/A | N/A |
| SEI CERT Oracle Coding Standard for Java | IDS00-J | Exact | Prevent SQL injection |
Taxonomy Name: PLOVER
Entry ID: N/A
Fit: N/A
Entry Name: SQL injection
Taxonomy Name: 7 Pernicious Kingdoms
Entry ID: N/A
Fit: N/A
Entry Name: SQL Injection
Taxonomy Name: CLASP
Entry ID: N/A
Fit: N/A
Entry Name: SQL injection
Taxonomy Name: OWASP Top Ten 2007
Entry ID: A2
Fit: CWE More Specific
Entry Name: Injection Flaws
Taxonomy Name: OWASP Top Ten 2004
Entry ID: A1
Fit: CWE More Specific
Entry Name: Unvalidated Input
Taxonomy Name: OWASP Top Ten 2004
Entry ID: A6
Fit: CWE More Specific
Entry Name: Injection Flaws
Taxonomy Name: WASC
Entry ID: 19
Fit: N/A
Entry Name: SQL Injection
Taxonomy Name: Software Fault Patterns
Entry ID: SFP24
Fit: N/A
Entry Name: Tainted input to command
Taxonomy Name: OMG ASCSM
Entry ID: ASCSM-CWE-89
Fit: N/A
Entry Name: N/A
Taxonomy Name: SEI CERT Oracle Coding Standard for Java
Entry ID: IDS00-J
Fit: Exact
Entry Name: Prevent SQL injection
▼Related Attack Patterns
| ID | Name |
|---|---|
| CAPEC-108 | Command Line Execution through SQL Injection |
| CAPEC-109 | Object Relational Mapping Injection |
| CAPEC-110 | SQL Injection through SOAP Parameter Tampering |
| CAPEC-470 | Expanding Control over the Operating System from the Database |
| CAPEC-66 | SQL Injection |
| CAPEC-7 | Blind SQL Injection |
ID: CAPEC-108
Name: Command Line Execution through SQL Injection
ID: CAPEC-109
Name: Object Relational Mapping Injection
ID: CAPEC-110
Name: SQL Injection through SOAP Parameter Tampering
ID: CAPEC-470
Name: Expanding Control over the Operating System from the Database
ID: CAPEC-66
Name: SQL Injection
ID: CAPEC-7
Name: Blind SQL Injection
▼References
Reference ID: REF-1460
Title: NT Web Technology Vulnerabilities
Author: rain.forest.puppy
Section:
Publication:
Phrack Issue 54, Volume 8
Publisher:
Edition:
URL Date:2025-03-14
Day:25
Month:12
Year:1998
Reference ID: REF-44
Title: 24 Deadly Sins of Software Security
Author: Michael Howard, David LeBlanc, John Viega
Section: "Sin 1: SQL Injection." Page 3
Publication:
McGraw-Hill
Publisher:
Edition:
URL:
URL Date:
Day:N/A
Month:N/A
Year:2010
Reference ID: REF-7
Title: Writing Secure Code
Author: Michael Howard, David LeBlanc
Section: Chapter 12, "Database Input Issues" Page 397
Publication:
Publisher:Microsoft Press
Edition:2nd Edition
URL Date:
Day:04
Month:12
Year:2002
Reference ID: REF-867
Title: SQL Injection Prevention Cheat Sheet
Author: OWASP
Section:
Publication:
Publisher:
Edition:
URL Date:
Day:N/A
Month:N/A
Year:N/A
Reference ID: REF-868
Title: SQL Injection Attacks by Example
Author: Steven Friedl
Section:
Publication:
Publisher:
Edition:
URL Date:
Day:10
Month:10
Year:2007
Reference ID: REF-869
Title: SQL Injection Cheat Sheet
Author: Ferruh Mavituna
Section:
Publication:
Publisher:
Edition:
URL:https://web.archive.org/web/20080126180244/http://ferruh.mavituna.com/sql-injection-cheatsheet-oku/
URL Date:2023-04-07
Day:15
Month:03
Year:2007
Reference ID: REF-870
Title: The Database Hacker's Handbook: Defending Database Servers
Author: David Litchfield, Chris Anley, John Heasman, Bill Grindlay
Section:
Publication:
Publisher:Wiley
Edition:
URL:
URL Date:
Day:14
Month:07
Year:2005
Reference ID: REF-871
Title: The Oracle Hacker's Handbook: Hacking and Defending Oracle
Author: David Litchfield
Section:
Publication:
Publisher:Wiley
Edition:
URL:
URL Date:
Day:30
Month:01
Year:2007
Reference ID: REF-872
Title: SQL Injection
Author: Microsoft
Section:
Publication:
Publisher:
Edition:
URL Date:2023-04-07
Day:N/A
Month:12
Year:2008
Reference ID: REF-873
Title: SQL Injection Attack
Author: Microsoft Security Vulnerability Research & Defense
Section:
Publication:
Publisher:
Edition:
URL Date:2023-04-07
Day:N/A
Month:N/A
Year:N/A
Reference ID: REF-874
Title: Giving SQL Injection the Respect it Deserves
Author: Michael Howard
Section:
Publication:
Publisher:
Edition:
URL Date:2023-04-07
Day:15
Month:05
Year:2008
Reference ID: REF-875
Title: Top 25 Series - Rank 2 - SQL Injection
Author: Frank Kim
Section:
Publication:
Publisher:SANS Software Security Institute
Edition:
URL Date:2023-04-07
Day:01
Month:03
Year:2010
Reference ID: REF-76
Title: Least Privilege
Author: Sean Barnum, Michael Gegick
Section:
Publication:
Publisher:
Edition:
URL Date:2023-04-07
Day:14
Month:09
Year:2005
Reference ID: REF-62
Title: The Art of Software Security Assessment
Author: Mark Dowd, John McDonald, Justin Schuh
Section: Chapter 8, "SQL Queries", Page 431
Publication:
Publisher:Addison Wesley
Edition:1st Edition
URL:
URL Date:
Day:N/A
Month:N/A
Year:2006
Reference ID: REF-62
Title: The Art of Software Security Assessment
Author: Mark Dowd, John McDonald, Justin Schuh
Section: Chapter 17, "SQL Injection", Page 1061
Publication:
Publisher:Addison Wesley
Edition:1st Edition
URL:
URL Date:
Day:N/A
Month:N/A
Year:2006
Reference ID: REF-962
Title: Automated Source Code Security Measure (ASCSM)
Author: Object Management Group (OMG)
Section: ASCSM-CWE-89
Publication:
Reference ID: REF-1447
Title: Secure by Design Alert: Eliminating SQL Injection Vulnerabilities in Software
Author: Cybersecurity and Infrastructure Security Agency
Section:
Publication:
Publisher:
Edition:
URL Date:2024-07-14
Day:25
Month:03
Year:2024
Details not found