CWE-307:Improper Restriction of Excessive Authentication Attempts
Weakness ID:307
Version:v4.17
Weakness Name:Improper Restriction of Excessive Authentication Attempts
Vulnerability Mapping:Allowed
Abstraction:Base
Structure:Simple
Status:Draft
Likelihood of Exploit:
▼Description
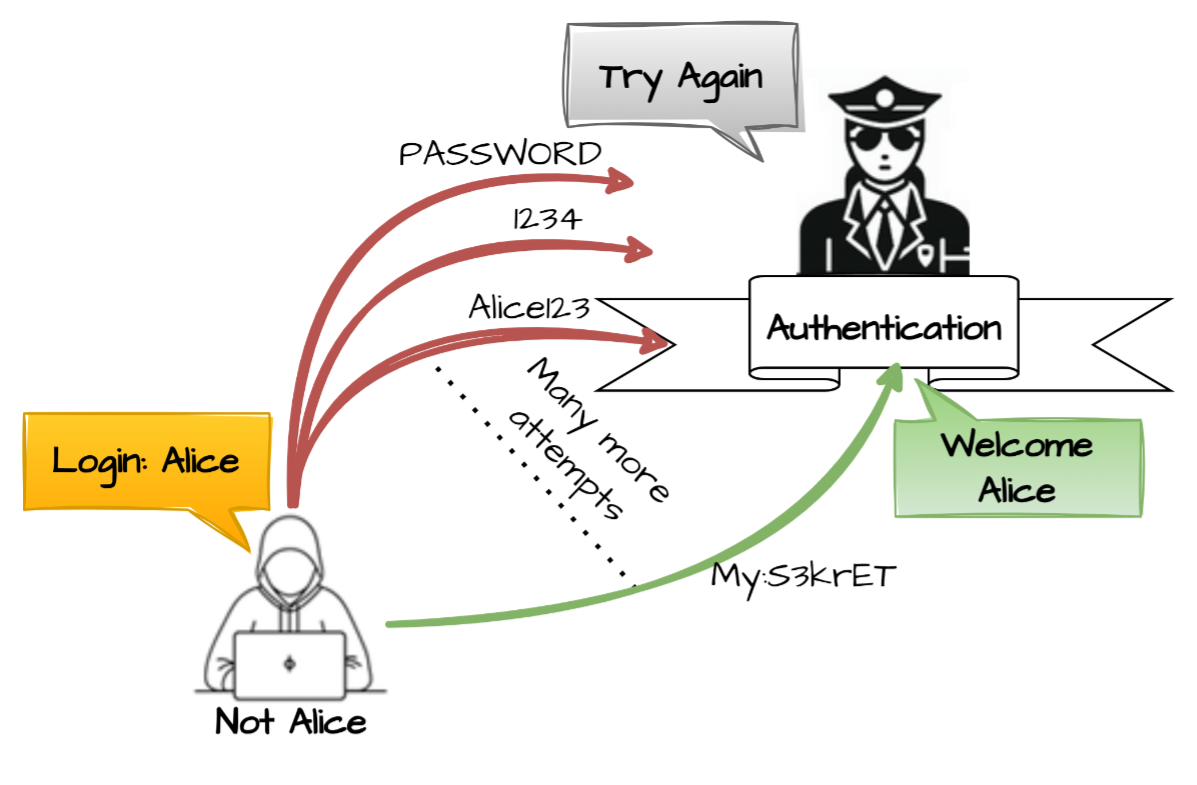
The product does not implement sufficient measures to prevent multiple failed authentication attempts within a short time frame.
▼Extended Description
▼Alternate Terms
▼Relationships
Relevant to the view"Research Concepts - (1000)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| ChildOf | Allowed-with-Review | C | 1390 | Weak Authentication |
| ChildOf | Allowed-with-Review | C | 799 | Improper Control of Interaction Frequency |
Nature: ChildOf
Mapping: Allowed-with-Review
Type: Class
ID: 799
▼Memberships
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 724 | OWASP Top Ten 2004 Category A3 - Broken Authentication and Session Management |
| MemberOf | Prohibited | C | 808 | 2010 Top 25 - Weaknesses On the Cusp |
| MemberOf | Prohibited | C | 812 | OWASP Top Ten 2010 Category A3 - Broken Authentication and Session Management |
| MemberOf | Prohibited | C | 866 | 2011 Top 25 - Porous Defenses |
| MemberOf | Prohibited | V | 884 | CWE Cross-section |
| MemberOf | Prohibited | C | 955 | SFP Secondary Cluster: Unrestricted Authentication |
| MemberOf | Prohibited | C | 1010 | Authenticate Actors |
| MemberOf | Prohibited | C | 1211 | Authentication Errors |
| MemberOf | Prohibited | C | 1353 | OWASP Top Ten 2021 Category A07:2021 - Identification and Authentication Failures |
| MemberOf | Prohibited | C | 1396 | Comprehensive Categorization: Access Control |
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 724
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 812
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 955
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1353
Nature: MemberOf
Mapping: Prohibited
Type:Category
ID: 1396
▼Tags
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | BS | BOSS-278 | Libraries or Frameworks Strategy |
| MemberOf | Prohibited | BS | BOSS-294 | Not Language-Specific Weaknesses |
| MemberOf | Prohibited | BS | BOSS-316 | Bypass Protection Mechanism (impact) |
Nature: MemberOf
Mapping: Prohibited
Type:BOSSView
ID: BOSS-316
▼Relevant To View
Relevant to the view"Architectural Concepts - (1008)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1010 | Authenticate Actors |
Relevant to the view"Software Development - (699)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1211 | Authentication Errors |
Relevant to the view"OWASP Top Ten (2021) - (1344)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 1353 | OWASP Top Ten 2021 Category A07:2021 - Identification and Authentication Failures |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 1353
Relevant to the view"Software Fault Pattern (SFP) Clusters - (888)"
| Nature | Mapping | Type | ID | Name |
|---|---|---|---|---|
| MemberOf | Prohibited | C | 955 | SFP Secondary Cluster: Unrestricted Authentication |
Nature: MemberOf
Mapping: Prohibited
Type: Category
ID: 955
▼Background Detail
▼Common Consequences
| Scope | Likelihood | Impact | Note |
|---|---|---|---|
| Access Control | N/A | Bypass Protection Mechanism | An attacker could perform an arbitrary number of authentication attempts using different passwords, and eventually gain access to the targeted account using a brute force attack. |
Scope: Access Control
Likelihood: N/A
Impact: Bypass Protection Mechanism
Note:
An attacker could perform an arbitrary number of authentication attempts using different passwords, and eventually gain access to the targeted account using a brute force attack.
▼Potential Mitigations
Phase:Architecture and Design
Mitigation ID:
Strategy:
Effectiveness:
Description:
Common protection mechanisms include:
- Disconnecting the user after a small number of failed attempts
- Implementing a timeout
- Locking out a targeted account
- Requiring a computational task on the user's part.
Note:
Phase:Architecture and Design
Mitigation ID: MIT-4
Strategy: Libraries or Frameworks
Effectiveness:
Description:
Use a vetted library or framework that does not allow this weakness to occur or provides constructs that make this weakness easier to avoid.
Consider using libraries with authentication capabilities such as OpenSSL or the ESAPI Authenticator. [REF-45]
Note:
▼Modes Of Introduction
Phase: Architecture and Design
Note:
COMMISSION: This weakness refers to an incorrect design related to an architectural security tactic.
▼Applicable Platforms
Languages
Class: Not Language-Specific(Undetermined Prevalence)
▼Demonstrative Examples
Example 1
In January 2009, an attacker was able to gain administrator access to a Twitter server because the server did not restrict the number of login attempts [REF-236]. The attacker targeted a member of Twitter's support team and was able to successfully guess the member's password using a brute force attack by guessing a large number of common words. After gaining access as the member of the support staff, the attacker used the administrator panel to gain access to 33 accounts that belonged to celebrities and politicians. Ultimately, fake Twitter messages were sent that appeared to come from the compromised accounts.
Language: ( code)
N/A
Language: ( code)
N/A
Example 2
The following code, extracted from a servlet's doPost() method, performs an authentication lookup every time the servlet is invoked.
Language: ( code)
N/A
Language: Java(Bad code)
String username = request.getParameter("username");
String password = request.getParameter("password");
int authResult = authenticateUser(username, password);
Language: ( code)
N/A
However, the software makes no attempt to restrict excessive authentication attempts.
Example 3
This code attempts to limit the number of login attempts by causing the process to sleep before completing the authentication.
Language: ( code)
N/A
Language: PHP(Bad code)
$username = $_POST['username'];
$password = $_POST['password'];
sleep(2000);
$isAuthenticated = authenticateUser($username, $password);
Language: ( code)
N/A
However, there is no limit on parallel connections, so this does not increase the amount of time an attacker needs to complete an attack.
Example 4
In the following C/C++ example the validateUser method opens a socket connection, reads a username and password from the socket and attempts to authenticate the username and password.
Language: ( code)
N/A
Language: C(Bad code)
int validateUser(char *host, int port)
{
int socket = openSocketConnection(host, port);
if (socket < 0) {
printf("Unable to open socket connection");
return(FAIL);
}
int isValidUser = 0;
char username[USERNAME_SIZE];
char password[PASSWORD_SIZE];
while (isValidUser == 0) {
if (getNextMessage(socket, username, USERNAME_SIZE) > 0) {
if (getNextMessage(socket, password, PASSWORD_SIZE) > 0) {
isValidUser = AuthenticateUser(username, password);
}
}
}
return(SUCCESS);
}
Language: ( code)
N/A
The validateUser method will continuously check for a valid username and password without any restriction on the number of authentication attempts made. The method should limit the number of authentication attempts made to prevent brute force attacks as in the following example code.
Language: C(Good code)
int validateUser(char *host, int port)
{
...
int count = 0;
while ((isValidUser == 0) && (count < MAX_ATTEMPTS)) {
if (getNextMessage(socket, username, USERNAME_SIZE) > 0) {
if (getNextMessage(socket, password, PASSWORD_SIZE) > 0) {
isValidUser = AuthenticateUser(username, password);
}
}
count++;
}
if (isValidUser) {
return(SUCCESS);
}
else {
return(FAIL);
}
}
Example 5
Consider this example from a real-world attack against the iPhone [REF-1218]. An attacker can use brute force methods; each time there is a failed guess, the attacker quickly cuts the power before the failed entry is recorded, effectively bypassing the intended limit on the number of failed authentication attempts. Note that this attack requires removal of the cell phone battery and connecting directly to the phone's power source, and the brute force attack is still time-consuming.
Language: ( code)
N/A
▼Observed Examples
| Reference | Description |
|---|---|
| CVE-2019-0039 | the REST API for a network OS has a high limit for number of connections, allowing brute force password guessing |
| CVE-1999-1152 | Product does not disconnect or timeout after multiple failed logins. |
| CVE-2001-1291 | Product does not disconnect or timeout after multiple failed logins. |
| CVE-2001-0395 | Product does not disconnect or timeout after multiple failed logins. |
| CVE-2001-1339 | Product does not disconnect or timeout after multiple failed logins. |
| CVE-2002-0628 | Product does not disconnect or timeout after multiple failed logins. |
| CVE-1999-1324 | User accounts not disabled when they exceed a threshold; possibly a resultant problem. |
Reference: CVE-2019-0039
Description:
the REST API for a network OS has a high limit for number of connections, allowing brute force password guessing
Reference: CVE-1999-1152
Description:
Product does not disconnect or timeout after multiple failed logins.
Reference: CVE-2001-1291
Description:
Product does not disconnect or timeout after multiple failed logins.
Reference: CVE-2001-0395
Description:
Product does not disconnect or timeout after multiple failed logins.
Reference: CVE-2001-1339
Description:
Product does not disconnect or timeout after multiple failed logins.
Reference: CVE-2002-0628
Description:
Product does not disconnect or timeout after multiple failed logins.
Reference: CVE-1999-1324
Description:
User accounts not disabled when they exceed a threshold; possibly a resultant problem.
▼Affected Resources
▼Functional Areas
▼Weakness Ordinalities
| Ordinality | Description |
|---|
▼Detection Methods
Dynamic Analysis with Automated Results Interpretation
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Web Application Scanner Web Services Scanner Database Scanners ``` Cost effective for partial coverage: ```
Host-based Vulnerability Scanners - Examine configuration for flaws, verifying that audit mechanisms work, ensure host configuration meets certain predefined criteria
Effectiveness:High
Note:
N/A
Dynamic Analysis with Manual Results Interpretation
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Fuzz Tester Framework-based Fuzzer ``` Cost effective for partial coverage: ```
Forced Path Execution
Effectiveness:High
Note:
N/A
Manual Static Analysis - Source Code
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Focused Manual Spotcheck - Focused manual analysis of source Manual Source Code Review (not inspections)
Effectiveness:High
Note:
N/A
Automated Static Analysis - Source Code
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Cost effective for partial coverage: ```
Source code Weakness Analyzer Context-configured Source Code Weakness Analyzer
Effectiveness:SOAR Partial
Note:
N/A
Automated Static Analysis
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Cost effective for partial coverage: ```
Configuration Checker
Effectiveness:SOAR Partial
Note:
N/A
Architecture or Design Review
Detection Method ID:
Description:
According to SOAR, the following detection techniques may be useful:
``` Highly cost effective: ```
Formal Methods / Correct-By-Construction ``` Cost effective for partial coverage: ```
Inspection (IEEE 1028 standard) (can apply to requirements, design, source code, etc.)
Effectiveness:High
Note:
N/A
▼Vulnerability Mapping Notes
Usage:Allowed
Reason:Acceptable-Use
Rationale:
This CWE entry is at the Base level of abstraction, which is a preferred level of abstraction for mapping to the root causes of vulnerabilities.
Comments:
Carefully read both the name and description to ensure that this mapping is an appropriate fit. Do not try to 'force' a mapping to a lower-level Base/Variant simply to comply with this preferred level of abstraction.
Suggestions:
▼Notes
▼Taxonomy Mappings
| Taxonomy Name | Entry ID | Fit | Entry Name |
|---|---|---|---|
| PLOVER | AUTHENT.MULTFAIL | N/A | Multiple Failed Authentication Attempts not Prevented |
| Software Fault Patterns | SFP34 | N/A | Unrestricted authentication |
Taxonomy Name: PLOVER
Entry ID: AUTHENT.MULTFAIL
Fit: N/A
Entry Name: Multiple Failed Authentication Attempts not Prevented
Taxonomy Name: Software Fault Patterns
Entry ID: SFP34
Fit: N/A
Entry Name: Unrestricted authentication
▼Related Attack Patterns
| ID | Name |
|---|---|
| CAPEC-16 | Dictionary-based Password Attack |
| CAPEC-49 | Password Brute Forcing |
| CAPEC-560 | Use of Known Domain Credentials |
| CAPEC-565 | Password Spraying |
| CAPEC-600 | Credential Stuffing |
| CAPEC-652 | Use of Known Kerberos Credentials |
| CAPEC-653 | Use of Known Operating System Credentials |
ID: CAPEC-16
Name: Dictionary-based Password Attack
ID: CAPEC-49
Name: Password Brute Forcing
ID: CAPEC-560
Name: Use of Known Domain Credentials
ID: CAPEC-565
Name: Password Spraying
ID: CAPEC-600
Name: Credential Stuffing
ID: CAPEC-652
Name: Use of Known Kerberos Credentials
ID: CAPEC-653
Name: Use of Known Operating System Credentials
▼References
Reference ID: REF-45
Title: OWASP Enterprise Security API (ESAPI) Project
Author: OWASP
Section:
Publication:
Reference ID: REF-236
Title: Weak Password Brings 'Happiness' to Twitter Hacker
Author: Kim Zetter
Section:
Publication:
Publisher:
Edition:
URL Date:2023-04-07
Day:09
Month:01
Year:2009
Reference ID: REF-1218
Title: This Black Box Can Brute Force Crack iPhone PIN Passcodes
Author: Graham Cluley
Section:
Publication:
The Mac Security Blog
Publisher:
Edition:
URL Date:
Day:16
Month:03
Year:2015
Details not found