### Summary On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability. ### Details Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1. ### PoC 1. Create a project.  2. Upload a file containing the payload using the "Upload Files" function.   The following are the contents of the files used in the PoC ``` { "data": { "prompt": "labelstudio universe image", "images": [ { "value": "id123#0", "style": "margin: 5px", "html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>" } ] } } ``` 3. Select the text-to-image generation labeling template of Ranking and scoring   4. Select a task 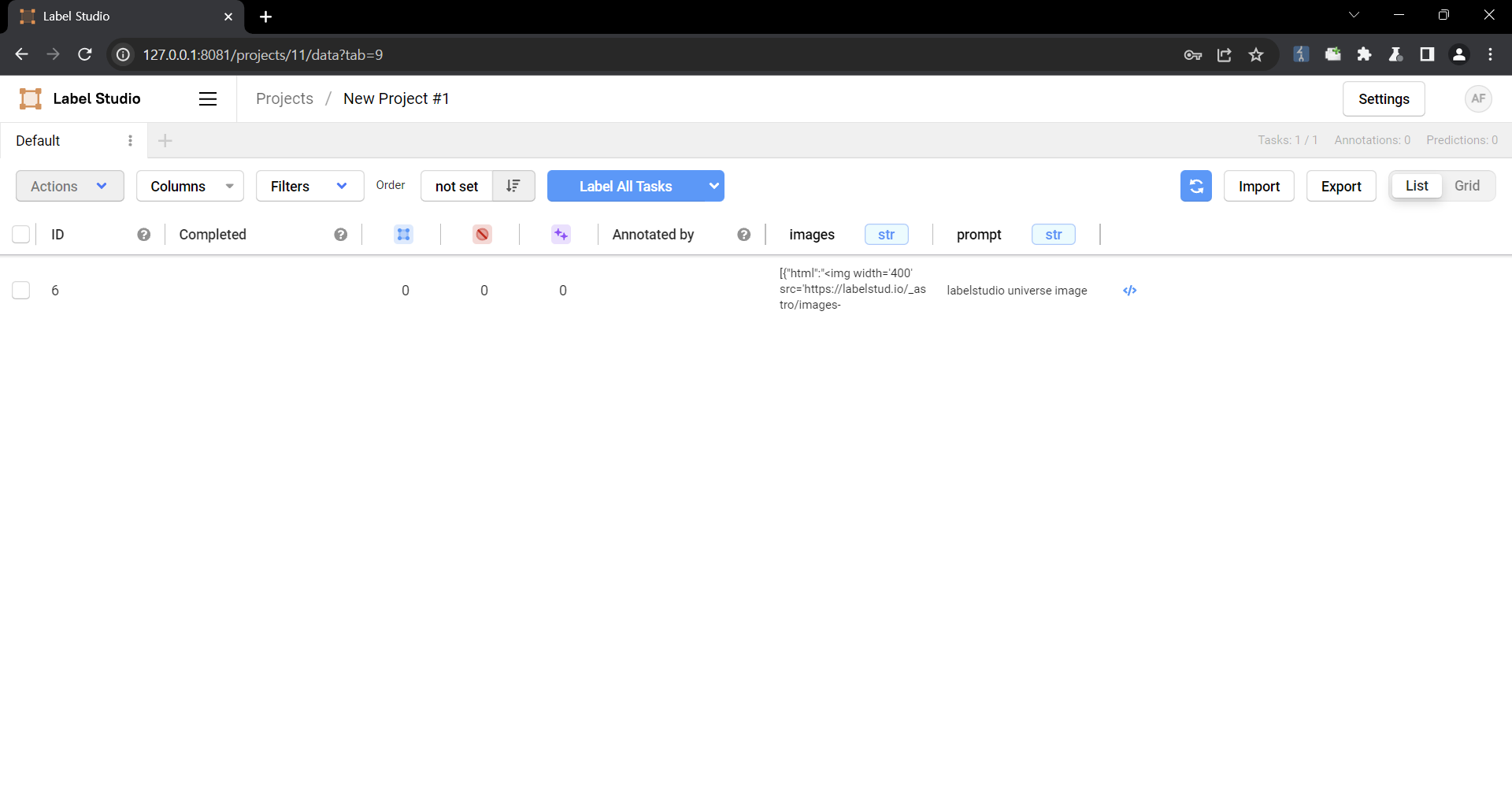 5. Check that the script is running 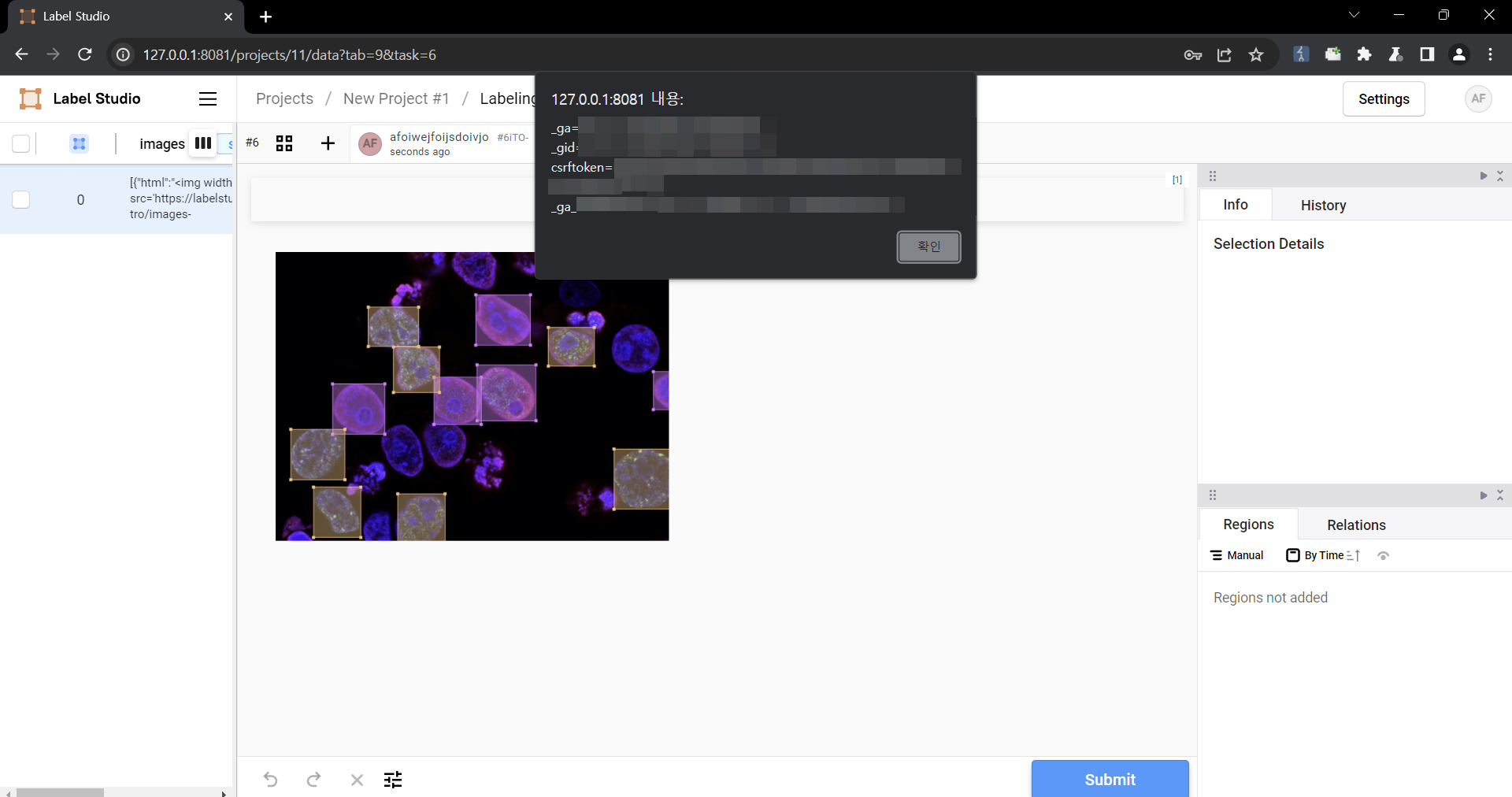 ### Impact Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.
Label Studio, an open source data labeling tool had a remote import feature allowed users to import data from a remote web source, that was downloaded and could be viewed on the website. Prior to version 1.10.1, this feature could had been abused to download a HTML file that executed malicious JavaScript code in the context of the Label Studio website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image. `data_import/uploader.py` lines 125C5 through 146 showed that if a URL passed the server side request forgery verification checks, the contents of the file would be downloaded using the filename in the URL. The downloaded file path could then be retrieved by sending a request to `/api/projects/{project_id}/file-uploads?ids=[{download_id}]` where `{project_id}` was the ID of the project and `{download_id}` was the ID of the downloaded file. Once the downloaded file path was retrieved by the previous API endpoint, `data_import/api.py`lines 595C1 through 616C62 demonstrated that the `Content-Type` of the response was determined by the file extension, since `mimetypes.guess_type` guesses the `Content-Type` based on the file extension. Since the `Content-Type` was determined by the file extension of the downloaded file, an attacker could import in a `.html` file that would execute JavaScript when visited. Version 1.10.1 contains a patch for this issue. Other remediation strategies are also available. For all user provided files that are downloaded by Label Studio, set the `Content-Security-Policy: sandbox;` response header when viewed on the site. The `sandbox` directive restricts a page's actions to prevent popups, execution of plugins and scripts and enforces a `same-origin` policy. Alternatively, restrict the allowed file extensions that may be downloaded.
Label Studio is a multi-type data labeling and annotation tool. A vulnerability in versions prior to 1.18.0 allows an attacker to inject a malicious script into the context of a web page, which can lead to data theft, session hijacking, unauthorized actions on behalf of the user, and other attacks. The vulnerability is reproducible when sending a properly formatted request to the `POST /projects/upload-example/` endpoint. In the source code, the vulnerability is located at `label_studio/projects/views.py`. Version 1.18.0 contains a patch for the issue.
Label Studio is a multi-type data labeling and annotation tool. In 1.22.0 and earlier, a persistent stored cross-site scripting (XSS) vulnerability exists in the custom_hotkeys functionality of the application. An authenticated attacker (or one who can trick a user/administrator into updating their custom_hotkeys) can inject JavaScript code that executes in other users’ browsers when those users load any page using the templates/base.html template. Because the application exposes an API token endpoint (/api/current-user/token) to the browser and lacks robust CSRF protection on some API endpoints, the injected script may fetch the victim’s API token or call token reset endpoints — enabling full account takeover and unauthorized API access.
Label Studio is an a popular open source data labeling tool. Versions prior to 1.9.2 have a cross-site scripting (XSS) vulnerability that could be exploited when an authenticated user uploads a crafted image file for their avatar that gets rendered as a HTML file on the website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image. The file `users/functions.py` lines 18-49 show that the only verification check is that the file is an image by extracting the dimensions from the file. Label Studio serves avatar images using Django's built-in `serve` view, which is not secure for production use according to Django's documentation. The issue with the Django `serve` view is that it determines the `Content-Type` of the response by the file extension in the URL path. Therefore, an attacker can upload an image that contains malicious HTML code and name the file with a `.html` extension to be rendered as a HTML page. The only file extension validation is performed on the client-side, which can be easily bypassed. Version 1.9.2 fixes this issue. Other remediation strategies include validating the file extension on the server side, not in client-side code; removing the use of Django's `serve` view and implement a secure controller for viewing uploaded avatar images; saving file content in the database rather than on the filesystem to mitigate against other file related vulnerabilities; and avoiding trusting user controlled inputs.
Auth0 is an authentication broker that supports both social and enterprise identity providers, including Active Directory, LDAP, Google Apps, and Salesforce. In versions before `11.33.0`, when the “additional signup fields” feature [is configured](https://github.com/auth0/lock#additional-sign-up-fields), a malicious actor can inject invalidated HTML code into these additional fields, which is then stored in the service `user_metdata` payload (using the `name` property). Verification emails, when applicable, are generated using this metadata. It is therefor possible for an actor to craft a malicious link by injecting HTML, which is then rendered as the recipient's name within the delivered email template. You are impacted by this vulnerability if you are using `auth0-lock` version `11.32.2` or lower and are using the “additional signup fields” feature in your application. Upgrade to version `11.33.0`.
An issue was discovered in Responsive Filemanager through 9.14.0. In the dialog.php page, the session variable $_SESSION['RF']["view_type"] wasn't sanitized if it was already set. This made stored XSS possible if one opens ajax_calls.php and uses the "view" action and places a payload in the type parameter, and then returns to the dialog.php page. This occurs because ajax_calls.php was also able to set the $_SESSION['RF']["view_type"] variable, but there it wasn't sanitized.
Chamilo 1.9.4 has Multiple XSS and HTML Injection Vulnerabilities: blog.php and announcements.php.
ForestBlog through 2022-02-16 allows admin/profile/save userAvatar XSS during addition of a user avatar.
kkFileView v4.0.0 was discovered to contain a cross-site scripting (XSS) vulnerability via the url parameter at /controller/OnlinePreviewController.java.
MajorDoMo (aka Major Domestic Module) contains a stored cross-site scripting (XSS) vulnerability through method parameter injection into the shoutbox. The /objects/?method= endpoint allows unauthenticated execution of stored methods with attacker-controlled parameters. Default methods such as ThisComputer.VolumeLevelChanged pass the user-supplied VALUE parameter directly into the say() function, which stores the message raw in the shouts database table without escaping. The shoutbox widget renders stored messages without sanitization in both PHP rendering code and HTML templates. Because the dashboard widget auto-refreshes every 3 seconds, the injected script executes automatically when any administrator loads the dashboard, enabling session hijack through cookie exfiltration.
Unauth. Reflected Cross-Site Scripting (XSS) vulnerability in weDevs WP ERP plugin <= 1.12.3 versions.
DIGISOL DG-HR3400 devices have XSS via a modified SSID when the apssid value is unchanged.
A vulnerability was detected in LigeroSmart up to 6.1.26. The impacted element is the function AgentDashboard of the file /otrs/index.pl. Performing a manipulation of the argument Subaction results in cross site scripting. Remote exploitation of the attack is possible. The exploit is now public and may be used. The project was informed of the problem early through an issue report but has not responded yet.
The cforms2 plugin before 14.13.3 for WordPress has multiple XSS issues.
MajorDoMo (aka Major Domestic Module) contains a stored cross-site scripting (XSS) vulnerability via the /objects/?op=set endpoint, which is intentionally unauthenticated for IoT device integration. User-supplied property values are stored raw in the database without sanitization. When an administrator views the property editor in the admin panel, the stored values are rendered without escaping in both a paragraph tag (SOURCE field) and a textarea element (VALUE field). The XSS fires on page load without requiring any click from the admin. Additionally, the session cookie lacks the HttpOnly flag, enabling session hijack via document.cookie exfiltration. An attacker can enumerate properties via the unauthenticated /api.php/data/ endpoint and poison any property with malicious JavaScript.
Cross-site scripting vulnerability in Cybozu Office 10.0.0 to 10.8.5 allows a remote attacker to inject an arbitrary script via unspecified vectors.
Unauth. Reflected Cross-Site Scripting (XSS) vulnerability in Robin Wilson bbp style pack plugin <= 5.5.5 versions.
A Cross Site Scripting vulnerability in PHPgurukl User Registration Login and User Management System with admin panel v.1.0 allows a local attacker to execute arbitrary code via a crafted script to the signup.php.
A weakness has been identified in LigeroSmart up to 6.1.26. Impacted is an unknown function of the file /otrs/index.pl?Action=AgentTicketSearch. This manipulation of the argument Profile causes cross site scripting. The attack may be initiated remotely. The exploit has been made available to the public and could be used for attacks. The project was informed of the problem early through an issue report but has not responded yet.
Frappe is a full-stack web application framework. Prior to 14.99.14 and 15.94.0, an attacker could craft a malicious signup URL for a frappe site which could lead to an open redirect (or reflected XSS, depending on the crafted payload) when a user signs up. This vulnerability is fixed in 14.99.14 and 15.94.0.
An issue was discovered in Mattermost Server before 3.8.2, 3.7.5, and 3.6.7. XSS can occur via a link on an error page.
NiceGUI is a Python-based UI framework. The ui.markdown() component uses the markdown2 library to convert markdown content to HTML, which is then rendered via innerHTML. By default, markdown2 allows raw HTML to pass through unchanged. This means that if an application renders user-controlled content through ui.markdown(), an attacker can inject malicious HTML containing JavaScript event handlers. Unlike other NiceGUI components that render HTML (ui.html(), ui.chat_message(), ui.interactive_image()), the ui.markdown() component does not provide or require a sanitize parameter, leaving applications vulnerable to XSS attacks. This vulnerability is fixed in 3.7.0.
Fabric.js is a Javascript HTML5 canvas library. Prior to version 7.2.0, Fabric.js applies `escapeXml()` to text content during SVG export (`src/shapes/Text/TextSVGExportMixin.ts:186`) but fails to apply it to other user-controlled string values that are interpolated into SVG attribute markup. When attacker-controlled JSON is loaded via `loadFromJSON()` and later exported via `toSVG()`, the unescaped values break out of XML attributes and inject arbitrary SVG elements including event handlers. Any application that accepts user-supplied JSON (via `loadFromJSON()`, collaborative sharing, import features, CMS plugins) and renders the `toSVG()` output in a browser context (SVG preview, export download rendered in-page, email template, embed) is vulnerable to stored XSS. An attacker can execute arbitrary JavaScript in the victim's browser session. Version 7.2.0 contains a fix.
Dify is an open-source LLM app development platform. Prior to 1.13.0, a cross site scripting vulnerability has been found in the web application chat frontend when using echarts. User or llm inputs containing echarts containing a specific javascript payload will be executed. This vulnerability is fixed in 1.13.0.
An issue was discovered in Mattermost Server before 4.0.0, 3.10.2, and 3.9.2. It allows XSS via an uploaded file.
The Formidable Form Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via multiple parameters submitted during form entries like 'after_html' in versions before 2.05.03 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts that execute in a victim's browser.
The weblibrarian plugin before 3.4.8.5 for WordPress has XSS via front-end short codes.
The Product Vendors is vulnerable to Reflected Cross-Site Scripting via the 'vendor_description' parameter in versions up to, and including, 2.0.35 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link.
SVXportal version 2.5 and prior contain a reflected cross-site scripting vulnerability in admin/log.php via the search query parameter. When an authenticated administrator views a crafted URL, the application embeds the unsanitized parameter value directly into an HTML input value attribute, allowing attacker-supplied JavaScript to execute in the administrator's browser. This can enable session theft, administrative action forgery, or other browser-based compromise in the context of an admin user.
The xmlrpc attacks blocker plugin for WordPress is vulnerable to Stored Cross-Site Scripting in versions up to, and including, 1.0, via the 'X-Forwarded-For' HTTP header. This is due to the plugin trusting and logging attacker-controlled IP header data and rendering debug log entries without output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts that execute when an administrator views the debug log page.
Leafkit is a templating language with Swift-inspired syntax. Prior to 1.4.1, htmlEscaped in leaf-kit will only escape html special characters if the extended grapheme clusters match, which allows bypassing escaping by using an extended grapheme cluster containing both the special html character and some additional characters. In the case of html attributes, this can lead to XSS if there is a leaf variable in the attribute that is user controlled. This vulnerability is fixed in 1.4.1.
MajorDoMo (aka Major Domestic Module) contains a reflected cross-site scripting (XSS) vulnerability in command.php. The $qry parameter is rendered directly into the HTML page without sanitization via htmlspecialchars(), both in an input field value attribute and in a paragraph element. An attacker can inject arbitrary JavaScript by crafting a URL with malicious content in the qry parameter.
Reflected Cross-site Scripting (XSS) in Alkacon's OpenCms v18.0, which allows an attacker to execute JavaScript code in the victim's browser by sending the victim a malicious URL containing the ‘q’ parameter in ‘/search/index.html’. This vulnerability can be exploited to steal sensitive user information such as session cookies, or to perform actions while impersonating the user.
The magic-fields plugin before 1.7.2 for WordPress has XSS via the RCCWP_CreateCustomFieldPage.php custom-group-id parameter.
Navidrome is an open source web-based music collection server and streamer. Prior to version 0.60.0, a cross-site scripting vulnerability in the frontend allows a malicious attacker to inject code through the comment metadata of a song to exfiltrate user credentials. This issue has been patched in version 0.60.0.
SVXportal version 2.5 and prior contain a stored cross-site scripting vulnerability in the user profile update workflow (user_settings.php submitting to admin/update_user.php). Authenticated users can store malicious HTML/JavaScript in fields such as Firstname, lastname, email, and image_url, which are later rendered without adequate output encoding in the administrator interface (admin/users.php), resulting in JavaScript execution in an administrator's browser when the affected page is viewed.
A vulnerability was found in Gwolle Guestbook Plugin 1.7.4. It has been rated as problematic. This issue affects some unknown processing. The manipulation leads to basic cross site scripting. The attack may be initiated remotely.
A vulnerability in the web-based management interface of Cisco Jabber Guest could allow an unauthenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the web-based management interface of an affected device. The vulnerability exists because the web-based management interface of the affected device does not properly validate user-supplied input. An attacker could exploit this vulnerability by persuading a user to click a malicious link. A successful exploit could allow the attacker to execute arbitrary script code in the context of the affected interface or to access sensitive, browser-based information. This vulnerability affects Cisco Jabber Guest releases 11.1(2) and earlier.
Asterisk is an open source private branch exchange and telephony toolkit. Prior to versions 20.7-cert9, 20.18.2, 21.12.1, 22.8.2, and 23.2.2, user supplied/control values for Cookies and any GET variable query Parameter are directly interpolated into the HTML of the page using ast_str_append. The endpoint at GET /httpstatus is the potential vulnerable endpoint relating to asterisk/main /http.c. This issue has been patched in versions 20.7-cert9, 20.18.2, 21.12.1, 22.8.2, and 23.2.2.
An XSS issue in the /goform/WifiBasicSet endpoint of Tenda AC15 AC1900 version 15.03.05.19 allows remote attackers to execute malicious payloads via the WifiName POST parameter.
A vulnerability, which was classified as problematic, has been found in Mail Subscribe List Plugin up to 2.0.10 on WordPress. This issue affects some unknown processing of the file index.php. The manipulation of the argument sml_name/sml_email leads to cross site scripting. The attack may be initiated remotely. Upgrading to version 2.1 is able to address this issue. The identifier of the patch is 484970ef8285cae51d2de3bd4e4684d33c956c28. It is recommended to upgrade the affected component. The identifier VDB-227765 was assigned to this vulnerability.
Firmware Analysis and Comparison Tool (FACT) 3 has Stored XSS when updating analysis details via a localhost web request, as demonstrated by mishandling of the tags and version fields in helperFunctions/mongo_task_conversion.py.
Certain NETGEAR devices are affected by reflected XSS. This affects M4300-28G before 12.0.2.15, M4300-52G before 12.0.2.15, M4300-28G-POE+ before 12.0.2.15, M4300-52G-POE+ before 12.0.2.15, M4300-8X8F before 12.0.2.15, M4300-12X12F before 12.0.2.15, M4300-24X24F before 12.0.2.15, M4300-24X before 12.0.2.15, M4300-48X before 12.0.2.15, and M4200 before 12.0.2.15.
SiYuan is self-hosted, open source personal knowledge management software. Prior to 3.5.4-dev2, a Stored Cross-Site Scripting (XSS) vulnerability exists in SiYuan Note. The application does not sanitize uploaded SVG files. If a user uploads and views a malicious SVG file (e.g., imported from an untrusted source), arbitrary JavaScript code is executed in the context of their authenticated session. This vulnerability is fixed in 3.5.4-dev2.
Movary is a web application to track, rate and explore your movie watch history. Due to insufficient input validation, attackers can trigger cross-site scripting payloads in versions prior to 0.70.0. The vulnerable parameter is `?categoryDeleted=`. Version 0.70.0 fixes the issue.
Movary is a web application to track, rate and explore your movie watch history. Due to insufficient input validation, attackers can trigger cross-site scripting payloads in versions prior to 0.70.0. The vulnerable parameter is `?categoryCreated=`. Version 0.70.0 fixes the issue.
WeGIA is a Web Manager for Charitable Institutions. Prior to 3.6.2, a Reflected Cross-Site Scripting (XSS) vulnerability was discovered in the WeGIA system, specifically within the html/memorando/insere_despacho.php file. The application fails to properly sanitize or encode user-supplied input via the id_memorando GET parameter before reflecting it into the HTML source (likely inside a <script> block or an attribute). This allows unauthenticated attackers to inject arbitrary JavaScript or HTML into the context of the user's browser session. This vulnerability is fixed in 3.6.2.
Improper handling of a URL parameter may allow attackers to execute code in a user's browser after login. This can lead to the extraction of sensitive data.
DOM-based Reflected Cross-Site Scripting (XSS) vulnerability in Elementor's Elementor Website Builder plugin <= 3.5.5 versions.